Your fintech platform is hemorrhaging money through security audit failures, and you're not alone. Nearly half of financial institutions reported breaches in the last 24 months, with the average cost hitting $5.90 million per incident.
This guide is for fintech CTOs, security engineers, and compliance teams who are tired of failing audits and need to understand what's actually breaking in their security architecture. You'll discover why common oversights like exposed APIs and weak access controls are costing companies millions in fines and lost trust.
We'll break down the most critical audit failure points, including PCI DSS compliance requirements that trip up even experienced teams and API security vulnerabilities that expose cardholder data in plain text. You'll also learn about structural security weaknesses that allow attackers to move laterally through your systems once they gain initial access.
By the end, you'll have a clear roadmap for implementing zero trust security implementation and fixing the specific gaps that cause audit failures before your next review cycle.
Understanding PCI DSS Requirements and Their Critical Importance
Core Payment Card Industry Data Security Standard framework
Your fintech platform operates within a complex regulatory environment where the Payment Card Industry Data Security Standard (PCI DSS) serves as the foundational security framework. This global standard was established by major payment brands including Visa, Mastercard, American Express, Discover, and JCB specifically to safeguard payment card data during every stage of processing, storage, and transmission.
When you're developing or managing a fintech platform, you must understand that PCI DSS compliance requirements aren't merely suggestions, they're mandatory security protocols that protect both your business and your customers' sensitive financial information. Your platform's architecture must be built around the framework's 12 core requirements, which are strategically organized into 6 overarching goals designed to create comprehensive protection for cardholder data.
The framework's structure ensures that your security measures address every potential vulnerability point where payment card data might be exposed. Each requirement builds upon the others to create a layered defense system that protects against both external threats and internal security weaknesses. Your compliance with these requirements directly impacts your ability to process payments and maintain your position in the financial services market.
Understanding this framework is crucial because it establishes the baseline security standards that your fintech security audit failures often stem from. When auditors examine your platform, they're measuring your implementation against these specific requirements, and any gaps in your compliance can result in immediate audit failures that compromise your business operations.
Key requirements for protecting cardholder data
Your fintech platform must implement specific PCI DSS requirements that directly govern how you handle sensitive payment card information. These requirements form the core of what auditors examine when assessing your security compliance standards.
Requirement 3.2 mandates that you must not store sensitive authentication data after authorization is complete. This means your platform cannot retain critical security elements such as CVV/CVC codes or full track data once a transaction has been authorized. Many fintech platforms fail security audits because their systems inadvertently cache or log this sensitive information, creating unnecessary security risks and direct compliance violations.
Your display mechanisms must comply with Requirement 3.3, which requires you to mask the Primary Account Number (PAN) whenever it appears in your user interfaces or reports. When displaying cardholder data, you can only show the last four digits of the card number, ensuring that sensitive information isn't exposed to unauthorized personnel or systems. This requirement often catches fintech platforms off-guard, particularly in administrative interfaces where full card numbers might seem necessary for operations.
Requirement 3.4 establishes that you must render PAN unreadable wherever it's stored or transmitted within your platform. Your implementation options include encryption, hashing, or tokenization—but the key principle is that raw card numbers should never exist in readable form within your systems. This requirement extends to databases, log files, backup systems, and any transmission channels your platform uses to communicate cardholder data.
These requirements directly address the most common fintech platform security weaknesses that lead to audit failures. Your platform's failure to properly implement any of these protections creates immediate compliance gaps that auditors will identify and flag as critical security deficiencies.
Financial and reputational consequences of non-compliance
Your non-compliance with PCI DSS requirements exposes your fintech platform to severe financial penalties that can devastate your business operations. Regulatory fines can reach up to $500,000 per incident, and these penalties multiply with each violation discovered during security audits. When your platform fails compliance standards, you're not just facing one-time fines—you're potentially exposing yourself to ongoing financial liability for every transaction processed while non-compliant.
Beyond immediate fines, your platform faces the risk of massive payment fraud exposure when security controls fail. Non-compliant systems become attractive targets for cybercriminals who can exploit the weaknesses that led to your audit failures. The financial impact of fraud incidents often exceeds the initial compliance fines, particularly when customer data is compromised and you become liable for fraudulent transactions and identity theft recovery costs.
Your merchant processing privileges are at immediate risk when you fail PCI DSS compliance requirements. Payment brands can revoke your ability to process credit card transactions, effectively shutting down your fintech platform's core revenue streams. This consequence is particularly devastating for fintech companies, as payment processing capabilities are fundamental to your business model and customer value proposition.
The reputational damage from compliance failures creates long-lasting consequences that extend far beyond immediate financial penalties. Your customers trust you with their most sensitive financial information, and news of security audit failures or data breaches can irreversibly damage that trust. Customer trust, once lost, is extremely difficult to rebuild in the competitive fintech market where security concerns heavily influence customer decisions.
Your platform's reputation in the financial services industry suffers when compliance failures become known to partners, investors, and regulatory bodies. This reputational damage can impact your ability to secure funding, establish partnerships with banks and financial institutions, and attract top-tier talent who want to work for reputable, compliant organizations.
Common API Security Vulnerabilities That Cause Audit Failures
Exposed Primary Account Numbers in API responses
Your fintech platform's API responses may be inadvertently exposing complete Primary Account Numbers (PANs), creating a critical security vulnerability that directly violates PCI DSS Requirement 3.4. This requirement explicitly mandates that all cardholder data must be rendered unreadable whenever it's stored or transmitted within your system architecture.
When your API endpoints return full credit card numbers in their responses, you're essentially broadcasting sensitive financial information that could be intercepted by malicious actors. Your development team might assume that because the API calls are internal or seemingly secure, exposing the complete PAN is acceptable. However, this misconception leads to immediate audit failures and puts your entire platform at significant compliance risk.
The core issue stems from your API design philosophy. If your endpoints are returning complete 16-digit card numbers instead of tokenized or masked versions, you're creating multiple attack vectors. Network traffic analysis, log file examination, or even simple debugging sessions could expose this sensitive data to unauthorized individuals within or outside your organization.
Your security auditors will flag this violation immediately because PCI DSS Requirement 3.4 doesn't provide exceptions for "internal" API communications. Every transmission of cardholder data must implement proper masking, truncation, or tokenization protocols to ensure the actual PAN remains protected throughout your system's data flow.
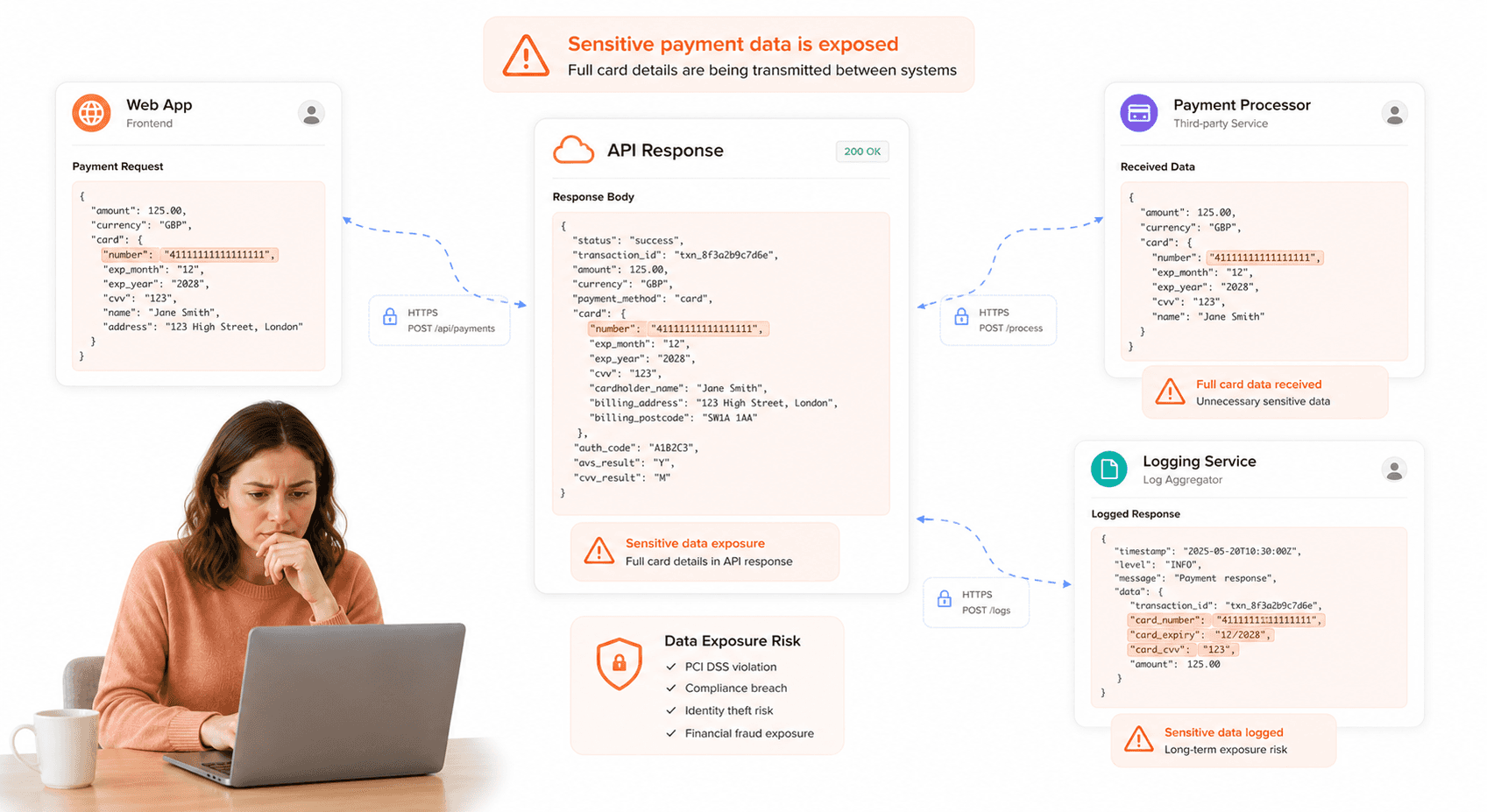
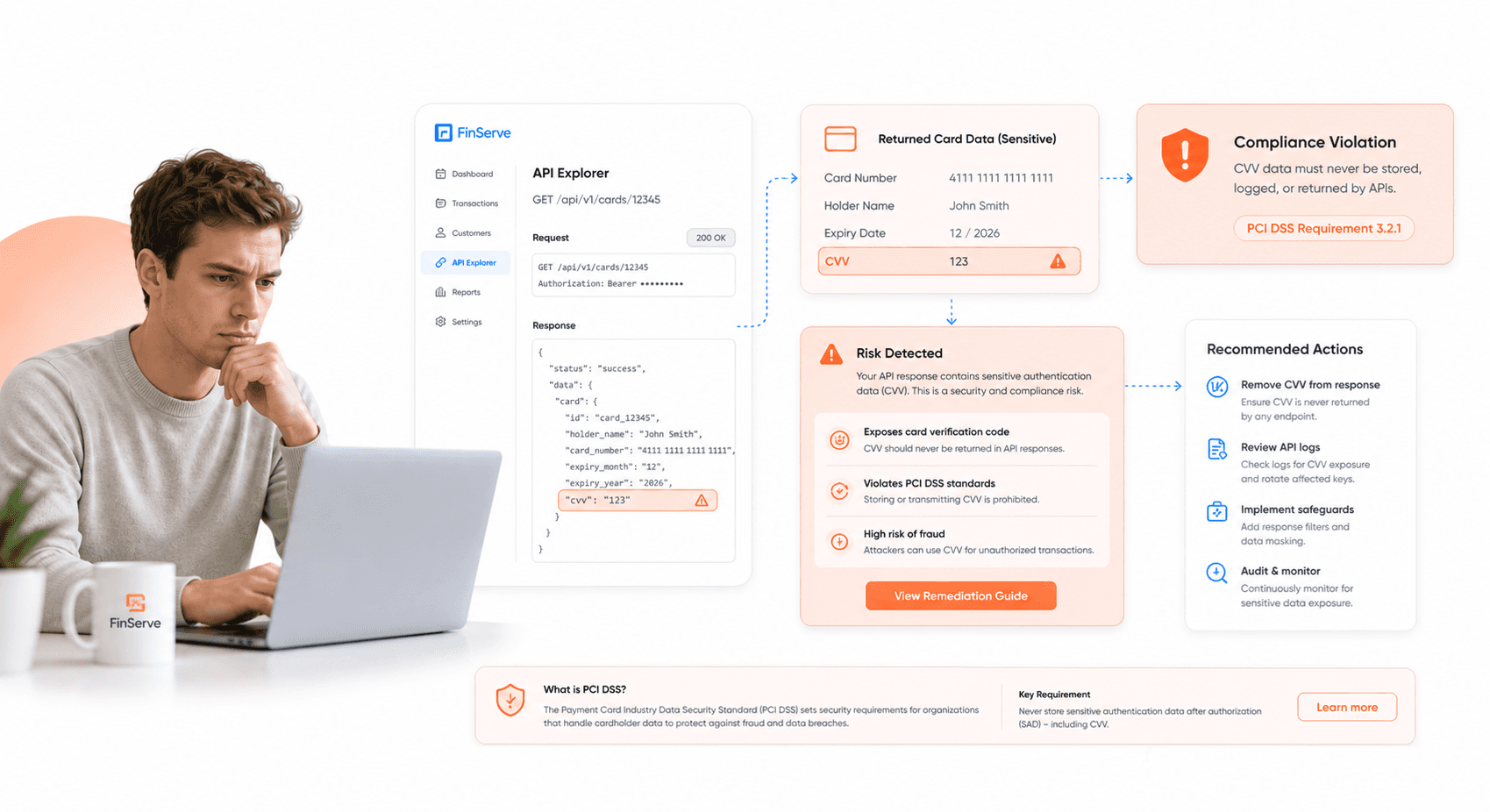
CVV data transmission violations
Your platform's API security vulnerabilities become even more severe when endpoints transmit Card Verification Values (CVV) in their responses. This practice represents one of the most serious PCI DSS compliance violations your fintech platform can commit, directly contravening Requirement 3.2's absolute prohibition on storing or transmitting CVV data after the authorization process completes.
Common violation scenarios occur when your virtual card creation endpoints, such as /api/virtual-cards/create or /api/virtual-cards, return CVV values in their response payloads. Your development team might believe this data transmission is necessary for user experience or integration purposes, but PCI DSS standards provide no flexibility regarding CVV handling post-authorization.
The severity of this violation cannot be overstated. When your APIs transmit CVV data, you're not only failing your security audits but also exposing your platform to significant financial penalties and potential loss of payment processing privileges. Your payment processors and acquiring banks will view CVV transmission violations as fundamental security failures that require immediate remediation.
Your audit failures in this area typically result from insufficient developer training regarding PCI DSS requirements. Many development teams don't fully understand that CVV data has extremely restrictive handling requirements compared to other cardholder data elements. Once the initial payment authorization completes, your systems must never store, transmit, or otherwise handle CVV information.
Unencrypted sensitive data in transit
Your fintech platform's transmission of unprotected sensitive data represents a critical vulnerability that security auditors consistently identify during PCI DSS compliance assessments. When your APIs transmit full PANs and CVV data without proper TLS encryption, you're creating opportunities for data theft and fraudulent transactions that could devastate your platform's reputation and financial stability.
The fundamental security principle here involves ensuring that all communications containing sensitive financial data utilize robust encryption protocols. Your platform must implement TLS encryption for every API communication, regardless of whether the transmission occurs between internal services, external integrations, or client applications.
Your security audit failures often stem from inconsistent encryption implementation across different API endpoints. While your public-facing APIs might utilize proper TLS encryption, internal service-to-service communications sometimes lack adequate protection. This creates security gaps that auditors will identify and flag as major compliance violations.
The risk assessment becomes particularly concerning when you consider the potential for man-in-the-middle attacks, packet sniffing, and other interception techniques. When your sensitive data travels across networks without encryption, malicious actors can easily capture and exploit this information for fraudulent purposes.
Your implementation strategy must ensure that TLS encryption covers all data transmission scenarios, including database connections, message queue communications, and third-party service integrations. The necessity for comprehensive encryption extends beyond simply meeting compliance requirements; it represents fundamental security hygiene that protects your users' financial information and maintains your platform's credibility within the fintech ecosystem.
User Interface Security Flaws That Violate Compliance Standards
Full Card Number Display Without Masking
Your fintech platform may be inadvertently violating PCI DSS compliance requirements by displaying complete card numbers on user dashboards. When you show the full Primary Account Number (PAN) to users, you're directly breaching PCI DSS Requirement 3.3, which explicitly mandates that payment card numbers must be masked when displayed in any user interface.
The regulation requires that you mask all but the first six and last four digits of any card number shown to users. This means displaying card numbers in formats like "1234 56XX XXXX 5678" rather than the complete sequence. Your failure to implement proper masking creates immediate fintech security audit failures during compliance assessments.
When auditors examine your platform, they'll scrutinize every instance where card data appears on screen. If they discover unmasked PANs in user accounts, transaction histories, or administrative panels, your platform will fail this critical security audit compliance standard. The visibility of complete card numbers creates unnecessary exposure points that increase fraud risk exponentially.
Your development team must implement masking algorithms that automatically obscure sensitive digits before rendering any payment information to users. This protection should apply across all user interfaces, including mobile applications, web dashboards, and administrative tools. Without proper masking, you're essentially providing cybercriminals with complete payment credentials if they gain unauthorized access to user accounts.
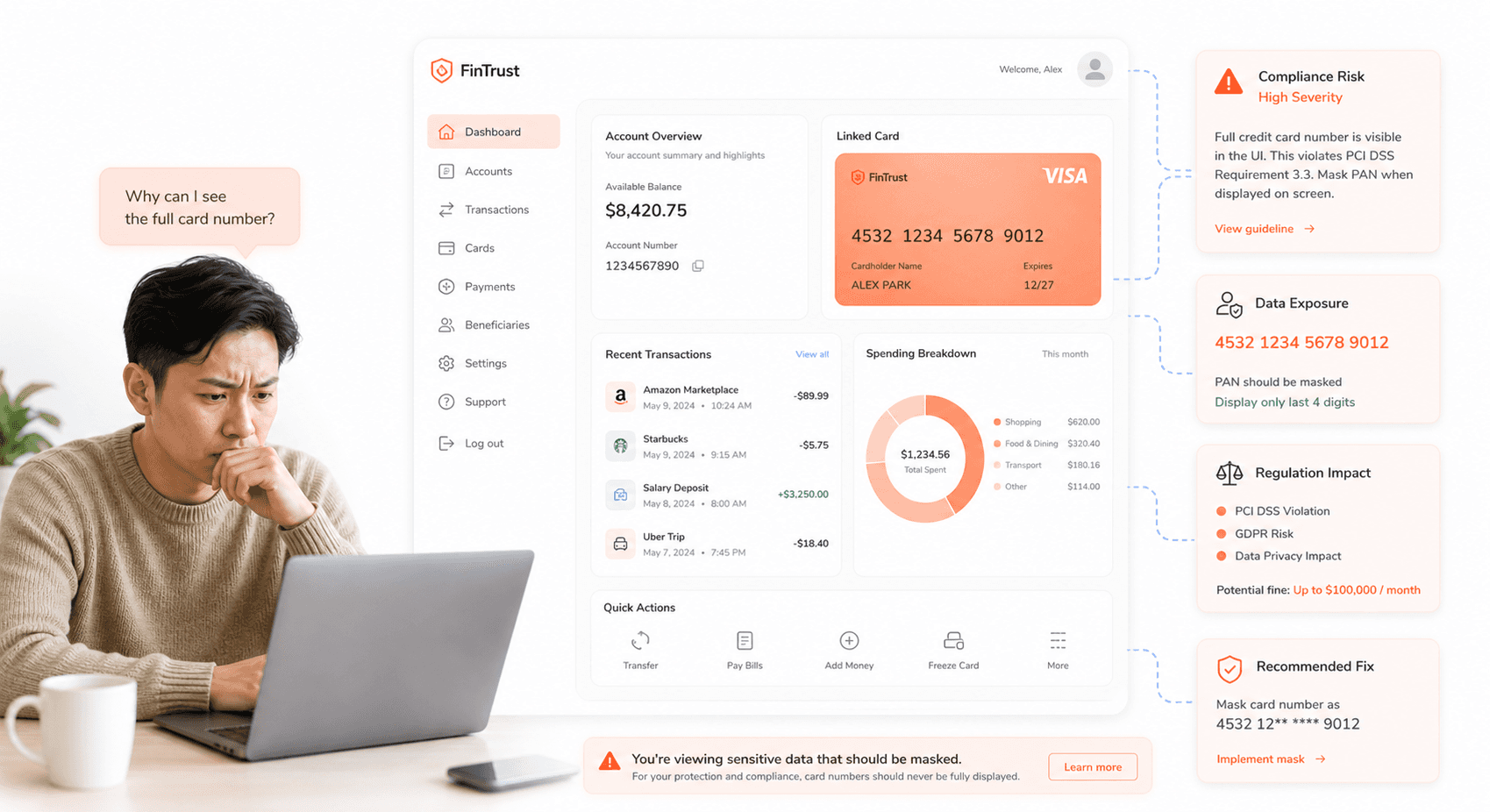
CVV Exposure on User Dashboards
Your platform faces severe fintech platform security weaknesses if CVV codes appear anywhere within user-accessible interfaces. PCI DSS Requirement 3.2 strictly prohibits the storage and display of CVV data, classifying it as sensitive authentication data that must only exist during the authorization process.
The three or four-digit CVV serves as a critical security layer for card-not-present transactions. When you expose CVV codes on dashboards, you're violating fundamental financial technology security flaws principles that auditors will immediately flag. This violation represents one of the most serious compliance failures, as CVV data should never persist in your systems beyond the initial transaction authorization window.
Your platform must ensure that CVV information is purged immediately after transaction processing. If your user interface displays stored CVV codes from previous transactions, you're creating a goldmine for fraudsters who compromise user accounts. Auditors will examine your data retention policies and user interface designs specifically to identify CVV exposure incidents.
The presence of CVV data in user dashboards indicates systemic security architecture problems within your platform. This suggests that your payment processing workflows lack proper data sanitization controls and that sensitive authentication data flows through systems where it shouldn't exist.
Browser Caching of Sensitive Payment Data
Your fintech platform creates significant third-party integration security risks when browsers cache sensitive cardholder information. Browser caching of payment data represents a critical vulnerability that enables fraud and identity theft, making prevention of such caching absolutely essential for maintaining security audit compliance standards.
When sensitive payment information gets cached in users' browsers, you're essentially storing confidential financial data in unsecured locations beyond your control. This cached data persists on user devices, creating potential access points for malicious actors who gain physical or remote access to those systems. Your platform must implement specific HTTP headers and caching directives that prevent browsers from storing any payment-related information.
The security implications extend beyond immediate fraud risks. Cached payment data can be extracted through browser forensics, shared across networks, or accessed by other applications running on user devices. Your failure to prevent caching demonstrates inadequate understanding of data flow security, which auditors will identify as a fundamental platform weakness.
Your development team must configure proper cache-control headers, implement no-store directives for sensitive pages, and ensure that payment forms use appropriate security attributes. Additionally, you should validate that your platform's SSL/TLS configuration prevents sensitive data from being cached at any point in the transmission chain.
Structural Security Weaknesses in Fintech Platforms
Over-privileged user accounts and service identities
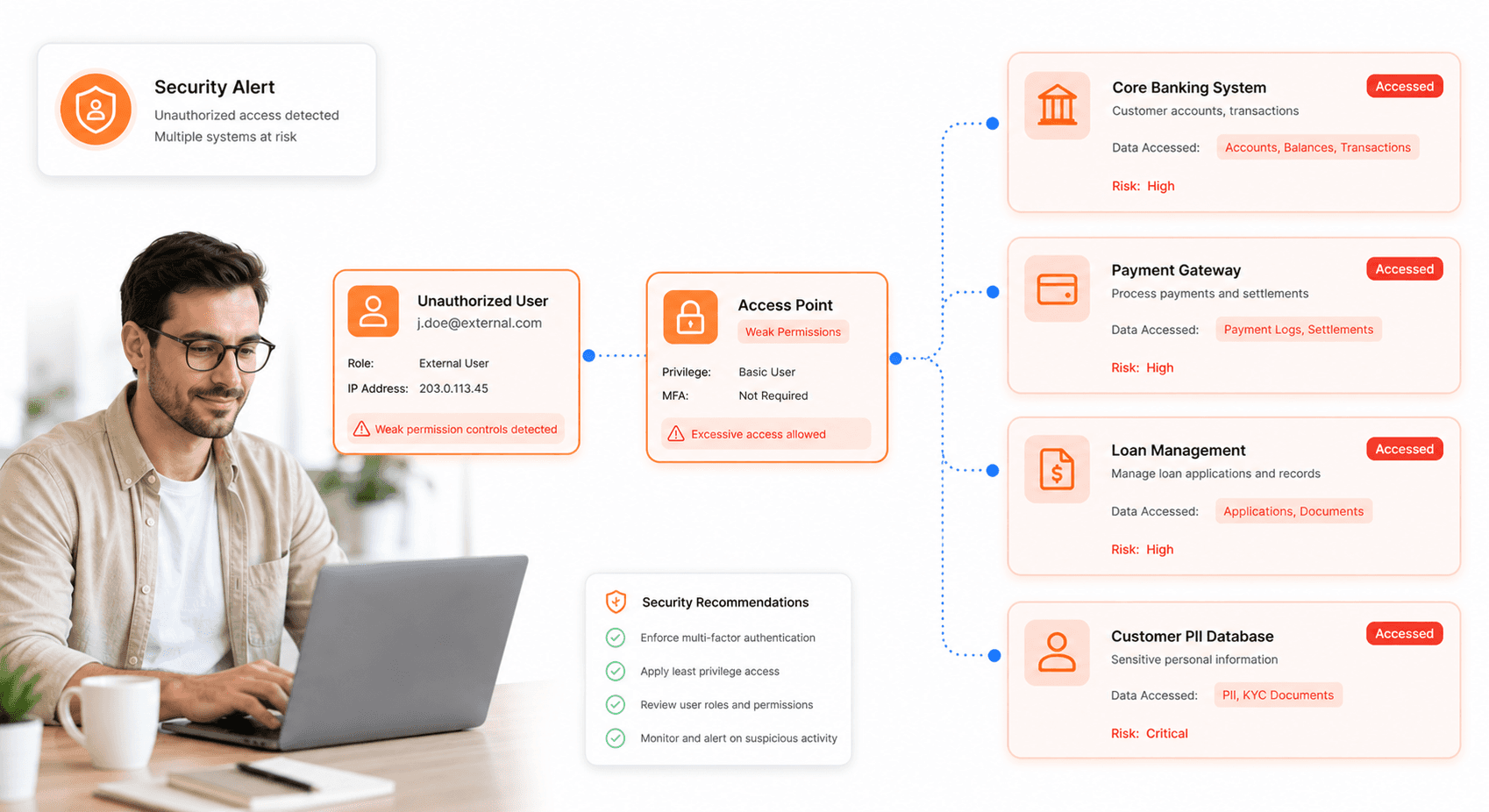
Your fintech platform's security foundation crumbles when user accounts and service identities accumulate excessive permissions over time. This privilege creep creates a significantly larger blast radius if any account becomes compromised, putting your entire financial ecosystem at risk. When you fail to regularly review and constrain access permissions, you're essentially handing attackers the keys to multiple systems simultaneously.
Service accounts pose an even greater threat in your fintech environment. These automated identities often receive broad permissions to facilitate system integrations and automated processes, but without proper governance, they become prime targets for attackers. Your development teams may grant extensive access during initial setup phases, then forget to reduce these permissions once systems are operational. This oversight leaves your platform vulnerable to lateral movement attacks where compromised service accounts become springboards for accessing sensitive financial data across multiple applications.
The cumulative effect of over-privileged accounts means that a single compromised credential can lead to extensive data breaches, unauthorized transactions, and complete system compromise. Your security auditors will flag these excessive permissions as critical fintech platform security weaknesses that directly violate principle of least privilege requirements.
Broken access control across applications and APIs
Your access control mechanisms represent one of the most critical fintech platform security weaknesses that consistently cause audit failures. When you implement inconsistent fine-grained authorization across your applications, APIs, services, and AI systems, you create dangerous gaps that allow authenticated users to exceed their intended scope of access.
This broken access control manifests in several ways within your fintech ecosystem. Authenticated users might gain unauthorized access to customer financial data belonging to other users, or they could perform payment actions that exceed their role-based permissions. Your API endpoints may lack proper authorization checks, allowing users with basic authentication to access administrative functions or sensitive financial operations.
The problem becomes more complex when you consider the interconnected nature of modern fintech platforms. Your mobile applications, web interfaces, backend APIs, and third-party integrations all need consistent access control policies. When these systems implement different authorization logic or fail to communicate permission boundaries effectively, you create opportunities for privilege escalation attacks.
Your security audit will reveal that broken access control represents a top application security risk because it directly impacts customer data protection and transaction integrity. Auditors specifically look for consistent authorization implementation across all touchpoints in your financial technology infrastructure.
Poor credential and token management practices
Your credential and token management practices often become the weakest link in your fintech security chain. When you implement long-lived tokens with broad scopes, you're essentially creating persistent attack vectors that give malicious actors extended access to your systems. These tokens, especially when they're insufficiently rotated or never expire, allow attackers to maintain access for weeks or months after initial compromise.
Your signing keys present another critical vulnerability point. When these cryptographic keys remain static for extended periods without proper rotation schedules, they become increasingly valuable targets for sophisticated attackers. The longer these keys remain unchanged, the more opportunities attackers have to compromise them through various attack vectors.
Token scope management represents a fundamental security principle that your platform must address. When you issue tokens with excessive permissions that go beyond what applications actually require, you're violating the principle of least privilege at the authentication layer. Your OAuth implementations, API keys, and session tokens should all follow strict scoping practices to limit potential damage from credential compromise.
The exposure period for compromised credentials directly correlates with your rotation policies and monitoring capabilities. Your fintech platform must implement automated credential rotation, comprehensive token lifecycle management, and real-time monitoring for suspicious credential usage patterns to meet compliance standards and pass security audits.
Internal System Vulnerabilities That Enable Lateral Movement
Weak Service-to-Service Authentication
Your fintech platform's internal service communications represent one of the most vulnerable attack vectors that security auditors scrutinize during compliance assessments. When your services validate workload identity only at the transport or token layer without enforcing proper resource-level authorization checks, you're essentially leaving the door wide open for lateral movement attacks that can devastate your entire infrastructure.
The fundamental issue lies in how your internal services handle authentication between themselves. You might have implemented what appears to be robust transport-layer security with proper token validation, but if your services aren't performing their own authorization checks beyond accepting these tokens, attackers who compromise one service can seamlessly move to others. This creates a domino effect where a single breach point becomes a gateway to your entire fintech platform security weaknesses.
Consider this scenario: your payment processing service accepts a valid token from your user management service, but it doesn't verify whether that specific token should actually have access to the particular payment data being requested. An attacker who has compromised the user management service can then leverage its legitimate tokens to access payment data that should be completely outside its operational scope. This type of vulnerability is precisely what causes fintech security audit failures during PCI DSS compliance assessments.
Your auditors will specifically look for evidence that each service maintains its own authorization logic rather than blindly trusting tokens from other internal services. They expect to see granular permission checks that verify not just "who" is making the request, but "what" they're allowed to access within the context of that specific service.
Insufficient Resource-Level Authorization Checks
Now that we've covered the authentication layer vulnerabilities, you need to understand how insufficient resource-level authorization checks compound these security risks. Even when your transport-level authentication appears functional, compromised workloads can still access additional internal APIs or modify critical financial data outside their intended operational boundaries.
Your authorization model must extend far beyond simple token validation. When your ledger service receives a request with a valid token, it should verify the specific account scope and transaction permissions associated with that token. Without this granular checking, a compromised service that legitimately holds a ledger service token can potentially access or modify financial records across multiple accounts, not just the ones it was designed to interact with.
This vulnerability becomes particularly dangerous in fintech environments where services often need to interact with sensitive financial data. Your customer onboarding service might legitimately need access to certain account creation APIs, but without proper resource-level checks, a compromise of this service could allow attackers to access existing account data or modify transaction histories they should never touch.
Security audit compliance standards require you to implement what's known as "principle of least privilege" at the resource level. This means every service request should be evaluated not just for valid authentication, but for specific authorization to access the exact resources being requested. Your audit trail should clearly demonstrate that each service interaction includes explicit permission verification for the specific data or operations involved.
Compromised Workload Exploitation Risks
With this in mind, next, we'll examine how compromised workload exploitation risks are significantly heightened by weak segmentation and overly broad service permissions. When your fintech platform lacks proper internal boundaries, security breaches can rapidly spread across systems that were never intended for direct exposure to external threats.
Your platform's segmentation strategy directly impacts your ability to contain security incidents. When services have broad permissions and weak network segmentation, a single compromised workload becomes a launching pad for accessing multiple internal systems. This creates a scenario where an attacker who gains access to your notification service, for example, can potentially pivot to your payment processing systems or customer data repositories.
The exploitation risk multiplies when your services operate with unnecessarily elevated privileges. Your fraud detection system might need read access to transaction data, but if it also has write permissions to customer profiles or system configurations, a compromise of this workload could allow attackers to not only access sensitive data but also modify security settings or customer information to facilitate further attacks.
Third-party integration security risks become particularly pronounced in this context. When your platform integrates with external services through internal workloads that have broad permissions, you're essentially extending your attack surface beyond your direct control. If these integration points lack proper resource-level authorization and operate within weakly segmented environments, external threats can more easily traverse your internal infrastructure.
Your security audit will evaluate whether your workload permissions follow strict necessity principles and whether your network segmentation effectively contains potential breaches. Auditors expect to see evidence that compromised workloads cannot easily access systems outside their operational requirements, and that your platform maintains multiple layers of authorization checks to prevent unauthorized lateral movement.
Third-Party Integration Security Gaps
Vendor dependency risks and API key exposure
Your fintech platform's reliance on third-party providers creates a complex web of vulnerabilities that can lead to devastating security audit failures. When you integrate with payment processors, cloud vendors, and other essential service providers, you're essentially extending your attack surface beyond your direct control. The critical risk emerges when vendor accounts become compromised or integration keys are leaked, potentially providing attackers with indirect access to your internal workflows.
Consider the implications of this exposure: if your payment processor's security is breached, attackers may gain access to API keys and authentication tokens that connect directly to your platform. These credentials often carry extensive permissions, allowing unauthorized parties to manipulate transactions, access customer data, or even initiate fraudulent activities under your platform's identity. Your security audit will inevitably fail when auditors discover that your third-party integration security risks haven't been properly mitigated.
The challenge intensifies when you realize that many fintech platforms store API keys in plain text configuration files or environment variables without proper encryption. This practice violates fundamental security audit compliance standards and creates multiple points of failure. Your vendors' security posture directly impacts your own compliance status, making vendor risk assessment a critical component of maintaining audit readiness.
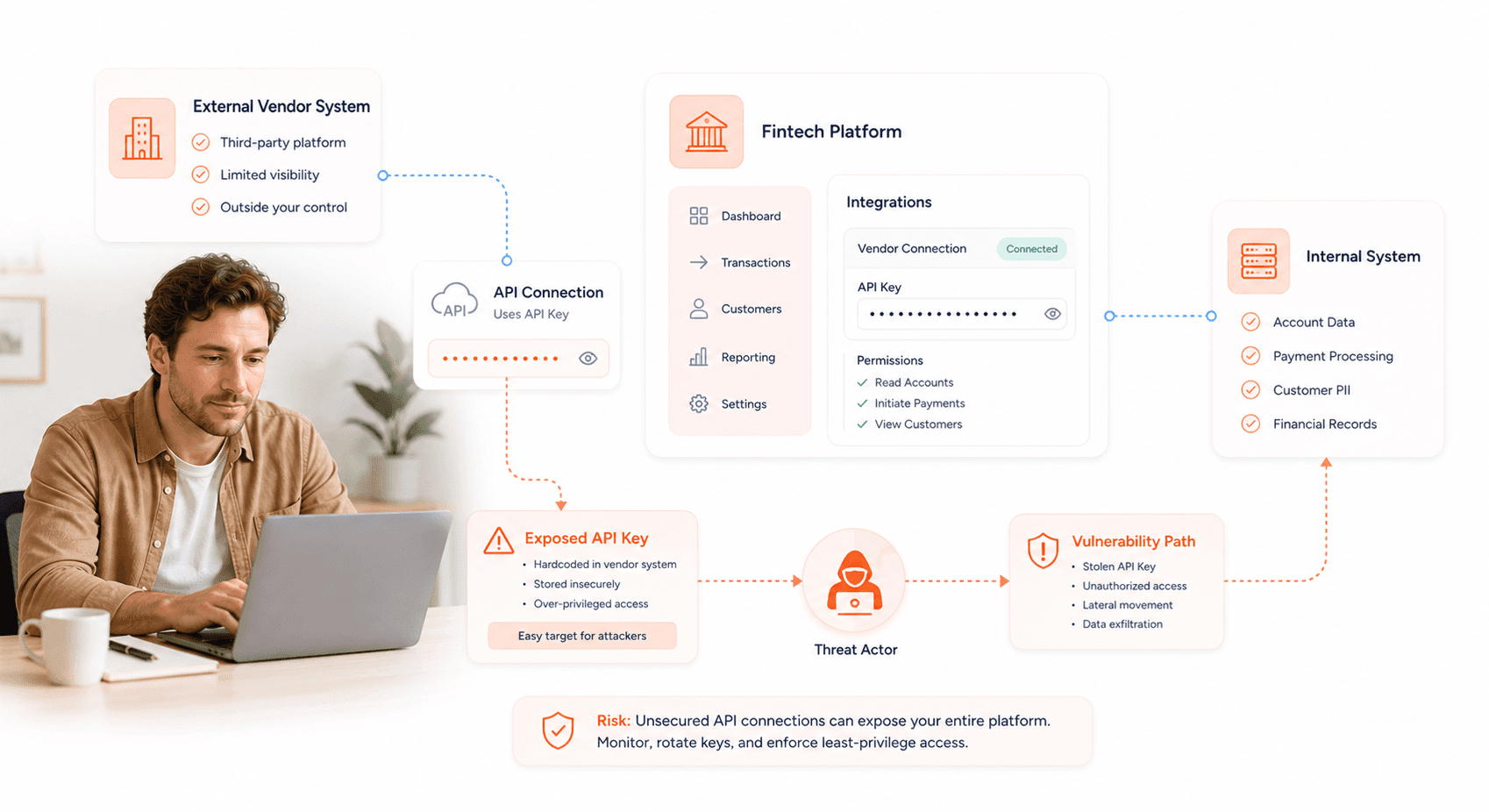
Inadequate webhook validation and monitoring
Moving beyond vendor risks, your webhook implementation represents another critical vulnerability that causes security audit failures. Webhooks serve as real-time communication channels between your platform and external services, but without proper validation and monitoring, they become open doors for malicious actors.
Your webhook endpoints must validate signatures from partner services to ensure message authenticity. When you fail to implement proper webhook signature validation, you're essentially accepting data from any source that can identify your endpoint URLs. This creates opportunities for attackers to inject false transaction data, manipulate account balances, or trigger unauthorized actions within your system.
Isolation of integration endpoints becomes crucial for maintaining security boundaries. Your webhook handlers should operate in segregated environments with limited access to core systems. Many fintech platforms fail audits because their webhook endpoints have excessive permissions or direct database access, violating the principle of least privilege.
Monitoring partner activity through your webhook infrastructure provides essential visibility into potential security breaches. Your audit logs should capture all webhook interactions, including failed validation attempts, unusual traffic patterns, and suspicious payload content. Without comprehensive monitoring, you cannot demonstrate to auditors that you maintain adequate oversight of third-party communications.
Supply chain vulnerability management failures
Your platform's security extends far beyond code you've written in-house. Supply chain exposure often originates from inherited code vulnerabilities in third-party libraries and dependencies. When you integrate external libraries into your application, you're inheriting their security flaws along with their functionality.
The most significant supply chain vulnerability management failures occur when fintech platforms neglect to scan their dependencies for known vulnerabilities. Your development team may unknowingly include libraries with critical security flaws, creating pathways for attackers to exploit your platform. These vulnerabilities often bypass your primary security controls because they exist within trusted code that your application relies upon.
Integrating dependency scanning and software composition analysis into your CI/CD pipelines becomes essential for detecting vulnerable third-party libraries before they reach production. Your deployment process should automatically identify outdated dependencies, known CVEs, and licensing issues that could impact your security posture. Many platforms fail security audits because they cannot demonstrate proactive management of their software supply chain.
Your vulnerability management strategy must include regular updates to third-party components and continuous monitoring of new security advisories. When critical vulnerabilities are discovered in your dependencies, you need established procedures for rapid assessment and remediation. Auditors will examine your ability to respond quickly to supply chain threats and maintain an accurate inventory of all third-party components in your technology stack.
Monitoring and Audit Trail Deficiencies
Insufficient logging of authorization decisions
Your fintech platform's authorization decisions represent the critical moments where your system determines whether to allow or deny access to sensitive financial data and transactions. When you fail to log these decisions adequately, you're essentially operating blind during the most crucial security events. This insufficient logging creates a cascade of problems that directly impact your ability to pass fintech security audit failures assessments.
The core issue lies in your system's inability to capture the complete context of each authorization event. You need to understand that auditors require detailed records showing not just what happened, but who performed the financial action and why your system allowed it at the specific time of the event. Without comprehensive logging, you cannot reconstruct these critical decision points during incident investigations or regulatory reviews.
Your authorization logs must capture multiple data points for each decision: the user identity making the request, the specific action attempted, the resource being accessed, the decision outcome, and the reasoning behind that outcome. When your logging mechanisms fail to capture any of these elements, you create gaps that make it impossible to demonstrate compliance with PCI DSS compliance requirements and other regulatory standards.
The problem becomes particularly acute during security incidents when you need to trace the sequence of events that led to a breach. Your incident response team requires complete visibility into the authorization chain to understand how an attacker gained access and what decisions your system made along the way. Insufficient logging transforms what should be a straightforward forensic investigation into a complex guessing game.
Limited visibility into access patterns
Your platform's access patterns tell a story about user behavior, system performance, and potential security threats. When you lack comprehensive visibility into these patterns, you're missing critical intelligence that could prevent fintech platform security weaknesses from being exploited by malicious actors.
Limited visibility manifests in several ways across your authorization infrastructure. You might be capturing individual authorization events but failing to correlate them into meaningful patterns that reveal the broader context of user activities. This fragmented view makes it extremely difficult to understand the rationale behind authorization decisions when you need to reconstruct events during a security incident investigation.
Your access pattern visibility should encompass temporal analysis of authorization requests, geographic distribution of access attempts, frequency patterns of resource requests, and behavioral baselines for individual users and roles. Without this comprehensive view, you cannot identify anomalous behavior that might indicate compromised accounts or insider threats targeting your financial systems.
The challenge becomes more complex when you consider that authorization decisions often depend on contextual factors beyond simple user credentials. Your system might grant access based on time of day, location, device characteristics, or transaction patterns. When you cannot see these contextual elements clearly, you lose the ability to validate whether your authorization decisions were appropriate for the given circumstances.
This limited visibility also hampers your ability to optimize your authorization policies. You need clear insights into how your current policies perform in real-world scenarios, which requests are being denied unnecessarily, and where your authorization logic might be creating friction for legitimate users while failing to block suspicious activities.
Regulatory compliance reporting gaps
Your regulatory reporting obligations demand precise documentation of every authorization decision your platform makes. These compliance reporting gaps represent some of the most serious deficiencies that cause fintech regulatory compliance failures during security audits. The standards you must meet, including PCI DSS, GDPR, and SOC 2, require comprehensive audit trails that demonstrate your platform's security controls are functioning as designed.
The regulatory framework expects you to log and audit every authorization decision with sufficient detail to meet these stringent standards. Your reporting gaps typically emerge when your logging infrastructure fails to capture essential elements like identity verification, action classification, resource identification, and outcome documentation. Each missing piece creates a compliance vulnerability that auditors will identify and flag as a significant deficiency.
Your audit trail must be immutable and tamper-evident to satisfy regulatory requirements. When you have gaps in your logging or insufficient detail in your authorization records, you cannot demonstrate that your security controls are operating effectively. Regulators need to see a complete chain of authorization decisions that proves your platform is protecting sensitive financial data according to established standards.
The challenge intensifies when you consider that different regulatory frameworks have varying requirements for authorization logging. PCI DSS requires specific documentation around payment card data access, while GDPR demands detailed records of personal data processing decisions. Your platform must capture authorization details that satisfy all applicable regulatory standards simultaneously.
Your compliance reporting gaps often become apparent only during formal audits when external assessors review your authorization logs and find them insufficient for regulatory purposes. By then, addressing these deficiencies requires significant remediation efforts that could have been avoided with proper logging architecture from the beginning.
Fraud Detection System Bypasses and Transaction Risks
Real-time transaction monitoring weaknesses
Your fraud detection system vulnerabilities can create significant security audit failures when real-time transaction monitoring lacks the sophistication needed for fintech compliance standards. These monitoring weaknesses directly expose your platform to attackers who execute multiple fraudulent financial actions before your systems can detect and respond to threats.
When your real-time monitoring systems fail to identify patterns quickly enough, attackers exploit these gaps to conduct card testing operations at scale. These attacks involve rapidly testing stolen credit card information through small transactions to identify valid cards, creating substantial financial exposure for your platform. The high volume of real-time transactions in fintech environments makes this particularly challenging, as legitimate transaction spikes can mask fraudulent activity patterns.
Your monitoring systems may also struggle with detecting payout loops, where attackers manipulate your platform's payout mechanisms to create circular money movements that drain funds over time. Without proper real-time detection capabilities, these sophisticated attacks can operate for extended periods, resulting in significant financial losses and compliance violations that trigger security audit failures.
The direct impact on your financial exposure becomes amplified due to the sheer volume of transactions your platform processes in real-time. Each undetected fraudulent transaction compounds your risk, making it essential to implement monitoring systems that can analyze transaction patterns, velocity, and behavioral anomalies within milliseconds of transaction initiation.
Rate limiting and abuse prevention failures
Your platform's rate limiting and abuse prevention failures represent critical transaction risks that auditors specifically examine during fintech security assessments. These failures enable attackers to scale common fraud patterns without adequate intervention, directly contributing to audit failures and regulatory compliance issues.
Bot-driven account creation presents a significant threat when your rate limiting controls are insufficient. Attackers can programmatically create thousands of accounts to establish networks for money laundering, synthetic identity fraud, and other financial crimes. Without proper rate limiting mechanisms, these automated attacks can overwhelm your systems and create substantial compliance risks that auditors will flag as major security deficiencies.
Your API abuse prevention measures must account for transaction volume scaling, as attackers often synchronize their attacks with peak transaction periods to avoid detection. When your rate limiting fails to adapt to legitimate traffic patterns while blocking malicious activity, it creates opportunities for fraud patterns to flourish during high-volume periods.
The relationship between rate limiting failures and transaction risks becomes particularly evident when attackers exploit your platform's API endpoints to conduct rapid-fire transactions or data harvesting operations. These attacks can manipulate transaction flows, extract sensitive financial data, or overwhelm your processing capabilities, all while flying under the radar of inadequate rate limiting controls.
AI agent authorization control gaps
Your emerging AI agent authorization control gaps represent a new frontier of fraud detection system vulnerabilities that auditors are increasingly scrutinizing. These gaps occur when broadly scoped or under-controlled AI agents connect to your internal systems without proper authorization boundaries, creating unprecedented risks for automated financial operations.
When your AI agents operate with excessive permissions, they can perform automated data retrieval operations that bypass traditional security controls. These agents might access customer financial data, transaction histories, or account information without proper oversight, creating compliance violations that directly impact your security audit outcomes.
Bulk queries executed by improperly controlled AI agents pose significant risks to your platform's data integrity and security posture. These agents can systematically extract large volumes of sensitive financial information, creating data breach scenarios that auditors will identify as critical security failures requiring immediate remediation.
Your unauthorized financial operations risk escalates dramatically when AI agents gain access to transaction processing systems without appropriate controls. These agents can initiate money transfers, modify account balances, or execute complex financial operations at machine speed and scale, translating directly into unauthorized money movement that represents both financial loss and severe compliance violations.
The scale at which AI agents operate makes these authorization control gaps particularly dangerous for your fintech platform security. Unlike human-driven attacks that are limited by manual processes, compromised or poorly controlled AI agents can execute thousands of unauthorized operations within minutes, creating cascading financial and compliance risks that sophisticated auditors will quickly identify as fundamental security architecture failures.
Implementing Zero Trust Security Controls
Step-up Authentication for High-Risk Operations
Your fintech platform's initial authentication shouldn't be the only security checkpoint protecting sensitive financial operations. When users attempt high-risk actions like payouts, limit changes, or bulk data exports, you need to implement step-up authentication that requires fresh authorization checks regardless of their current session status.
This approach moves beyond the dangerous assumption that initial login credentials provide sufficient security for all subsequent actions. Your platform should treat each sensitive operation as a new security event requiring additional verification. When a user tries to initiate a large wire transfer or modify account spending limits, your system should prompt for additional authentication factors, whether that's biometric verification, SMS codes, or hardware token validation.
The key principle here is treating high-risk operations as distinct security events that demand fresh credentials. Your audit compliance depends on demonstrating that sensitive financial actions receive proportional security measures. This means implementing dynamic risk assessment that evaluates the operation's potential impact and adjusts authentication requirements accordingly.
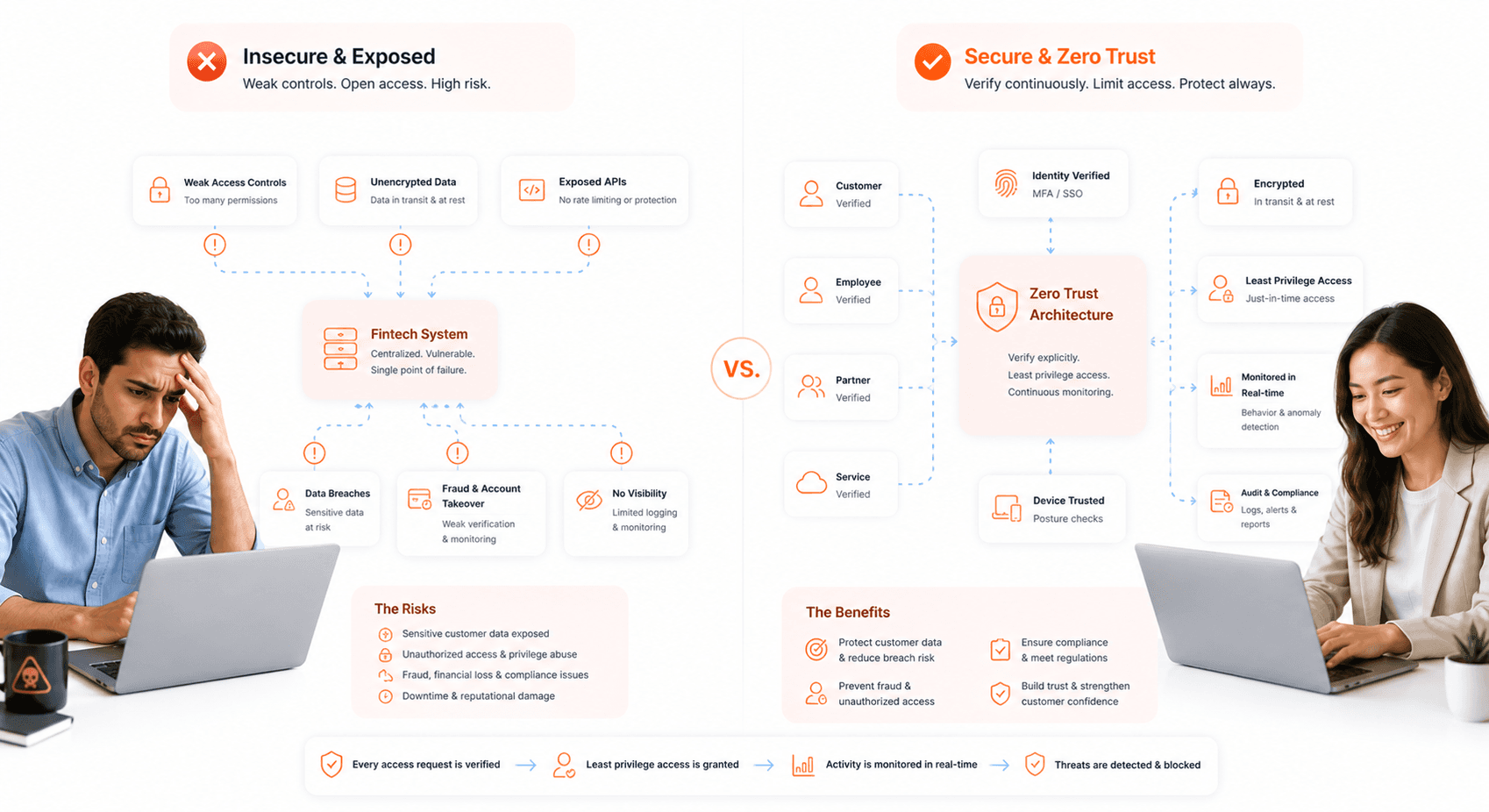
Fine-Grained Runtime Authorization Enforcement
Your authorization decisions must happen at runtime for every single protected request across your fintech platform. This means abandoning static permission models in favor of dynamic access controls that evaluate each request based on current context, user attributes, and the specific resource being accessed.
You need to implement narrowly defined permissions that apply consistently across all identities in your system, including human users, service accounts, and AI agents. Each entity should receive only the minimum permissions necessary for their specific functions, with no broad-stroke access grants that could enable unauthorized actions.
Your runtime authorization system should evaluate multiple contextual factors for each access request: the specific action being performed, the resource being accessed, the user's current role and department, the time of access, the location of the request, and any relevant business rules. This contextual access policy framework ensures that your zero trust security implementation adapts to changing circumstances and maintains security audit compliance standards.
The enforcement mechanism must operate consistently across your entire platform architecture, from API endpoints to database queries to third-party integrations. Every component should validate permissions at the moment of access rather than relying on inherited or cached authorization decisions.
Regular Access Reviews and Privilege Management
Your access management strategy requires ongoing attention to ensure permissions remain aligned with current employee responsibilities and business needs. Regular access reviews form the backbone of your privilege management program, helping you maintain compliance with fintech security audit requirements while minimizing security vulnerabilities.
You should implement systematic reviews that examine user permissions quarterly or whenever role changes occur. These reviews must verify that each user's access rights match their current job functions and remove any unnecessary privileges that have accumulated over time. This process becomes particularly critical in fintech environments where employees frequently change roles or departments.
Your privilege management framework must enforce the principle of least privilege consistently across all system components. This means granting users only the minimum access necessary to perform their specific job functions, with no additional permissions that could create security vulnerabilities or compliance violations.
Credential lifecycle management represents another crucial component of your access control strategy. Your system should utilize short-lived, narrowly scoped tokens that automatically expire after brief periods, forcing regular re-authentication and reducing the window of opportunity for credential compromise. These tokens should be scoped to specific functions or resources rather than providing broad system access.
Regular key rotation schedules minimize your exposure to credential compromise while maintaining operational continuity. Your automated rotation processes should update authentication keys, API tokens, and service account credentials on predetermined schedules, with immediate rotation capabilities for emergency situations where compromise is suspected.
Conclusion
The security vulnerabilities plaguing your fintech platform aren't just technical oversights, they represent fundamental failures in how you handle the most sensitive data your customers entrust to you. From exposed PAN and CVV data in API responses to unmasked payment details in user interfaces, these violations of PCI DSS requirements create direct pathways for attackers to commit massive fraud. When you combine these issues with over-privileged access controls, weak third-party integrations, and insufficient monitoring capabilities, you're essentially providing cybercriminals with a roadmap to your most valuable assets.
Your path to passing security audits requires immediate action across multiple fronts. Implement tokenization and encryption for all cardholder data, enforce least-privilege access controls for users and service accounts, strengthen your fraud detection systems, and establish comprehensive audit logging that meets regulatory requirements. Remember, security compliance isn't just about avoiding fines, it's about protecting the trust your customers place in you when they share their financial information. Start by addressing the most critical vulnerabilities first, then build a robust security framework that treats compliance as a foundation, not an afterthought.

About the author
I’m the founder of Hashbyt, an AI-first frontend and UI/UX SaaS partner helping 200+ SaaS companies scale faster through intelligent, growth-driven design. My work focuses on building modern frontend systems, design frameworks, and product modernization strategies that boost revenue, improve user adoption, and help SaaS founders turn their UI into a true growth engine.
Is a clunky UI holding back your growth?
Is a clunky UI holding back your growth?
▶︎
Transform slow, frustrating dashboards into intuitive interfaces that ensure effortless user adoption.
▶︎
Transform slow, frustrating dashboards into intuitive interfaces that ensure effortless user adoption.